The Essential Guide to Privilege Escalation Attacks
Hacking into a system and remaining a standard user can’t be too much fun. It would be like sneaking onto a private beach but only being allowed to build a sandcastle. If you want to do anything impactful (or harmful), you need a higher level of privilege. Privilege escalation helps attackers accomplish this goal, and they are increasingly common.
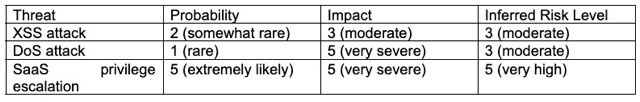
55% of insider attacks rely on privilege escalation exploits, where bad actors improperly gain higher “back end” access. Indeed, some of the worst cyberattacks, from WannaCry to NotPetya and BlueKeep, have occurred because of privilege escalation. Knowing how these attacks work is the first step in preventing and mitigating them.
Understanding Privilege Escalation Attacks
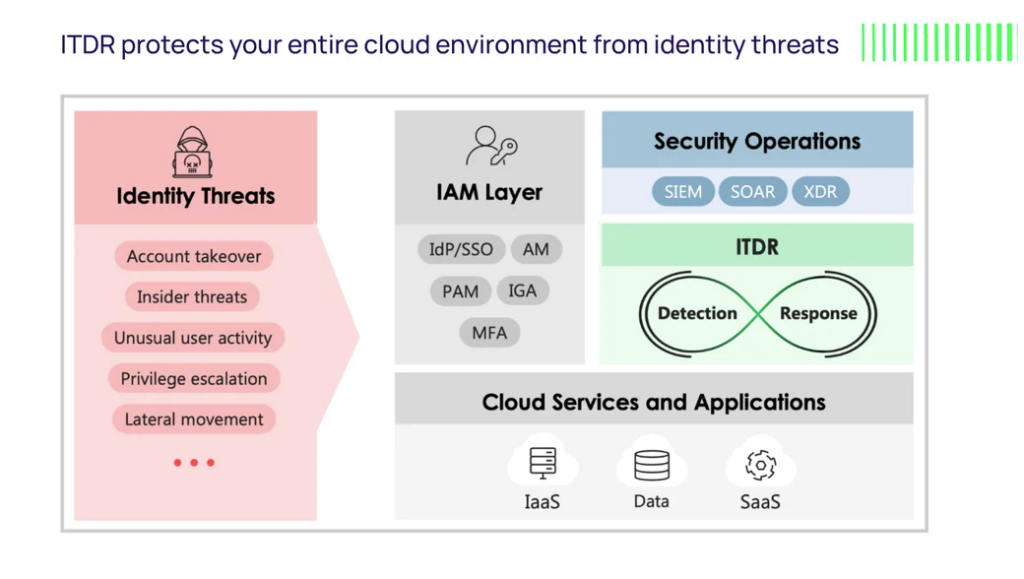
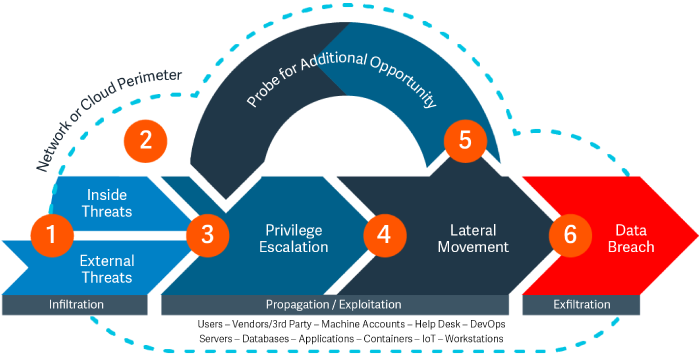
In a privilege escalation attack, a malicious actor (sometimes an insider) gains the privileges available to admin or super admin users. With these privileges, the attacker can disrupt the target system, cut off users, change passwords, install ransomware, or breach its data.
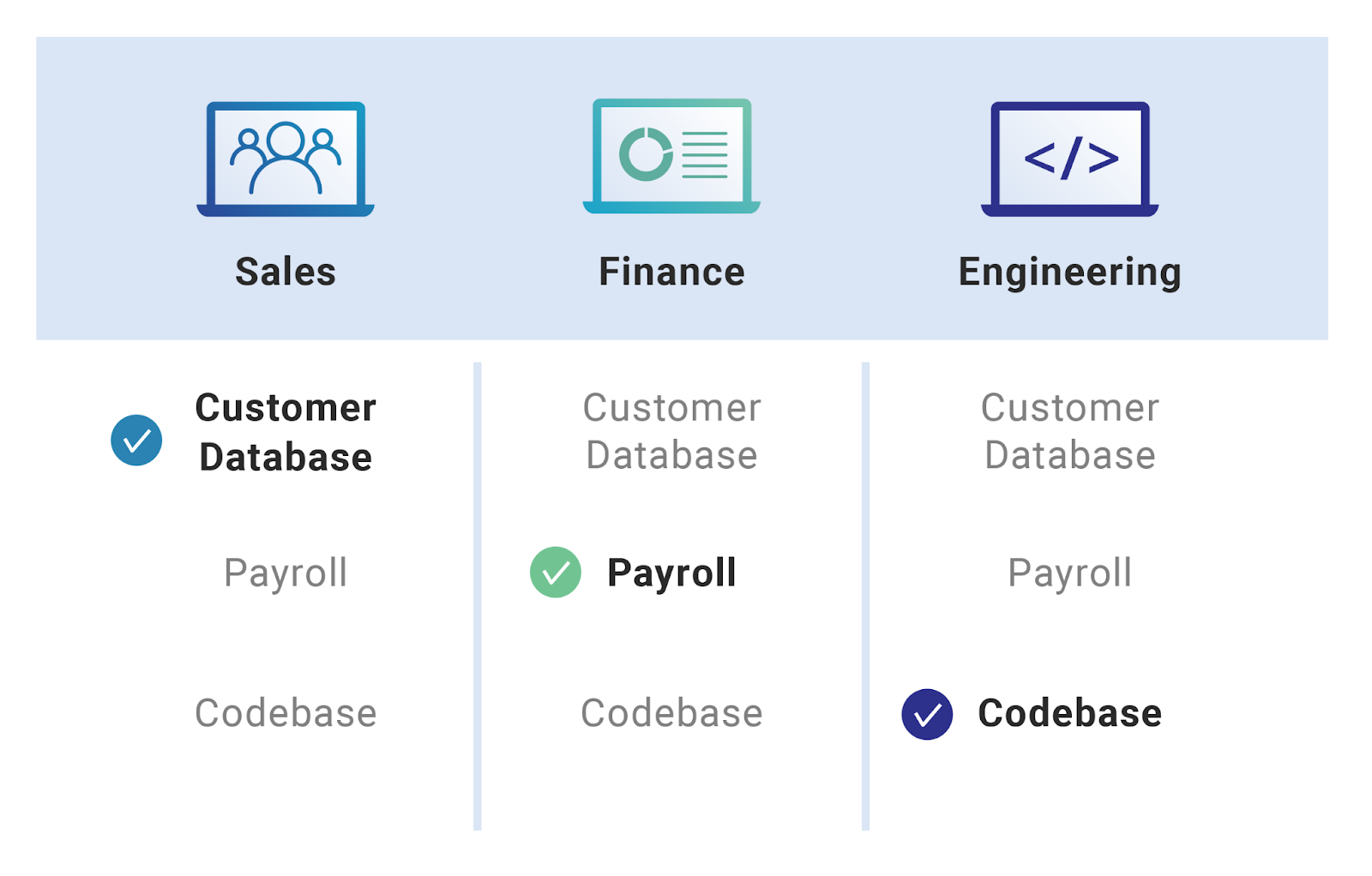
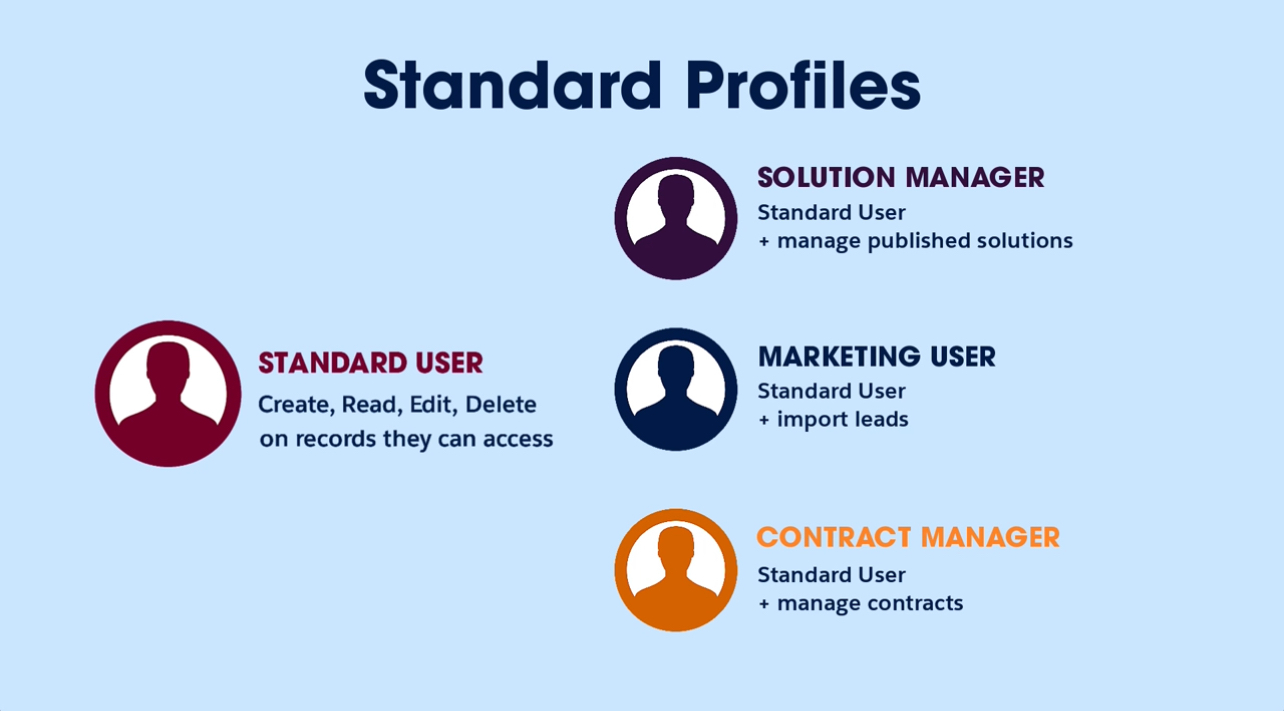
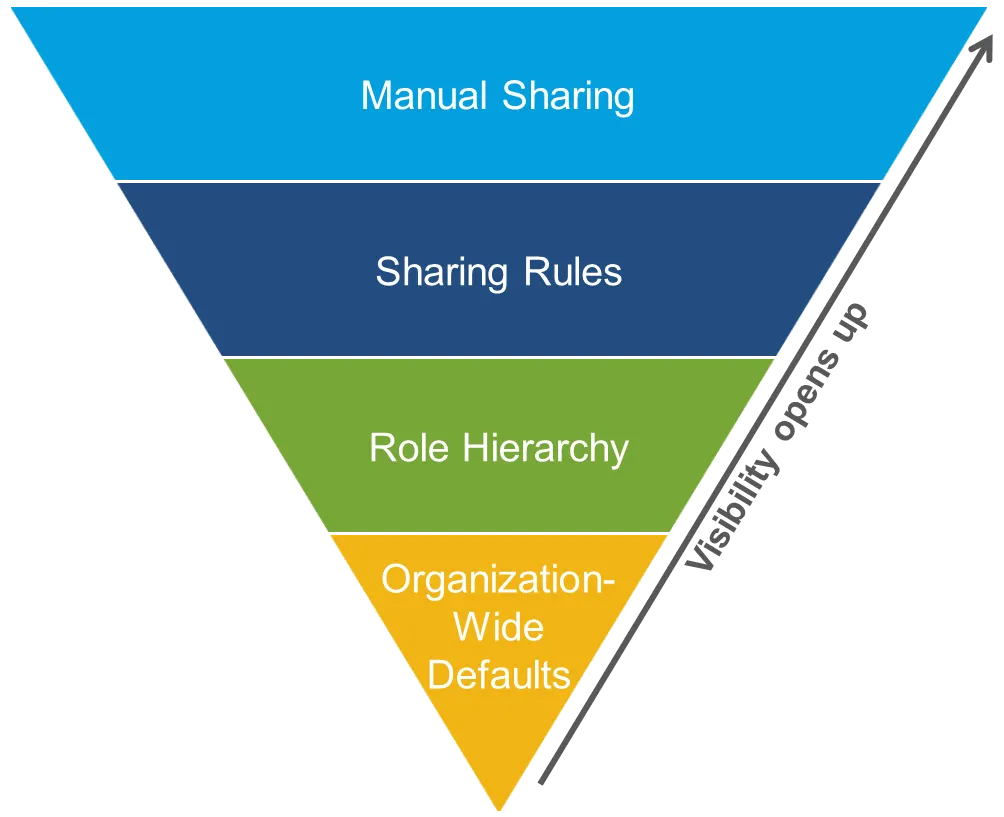
To understand privilege escalation attacks better, it helps to be familiar with the general concept of privilege in computer systems. Virtually all computer systems have a front end, which offers features for use by the public or standard users. For example, users can access basic functionality like looking up a customer’s address within their Salesforce environment or other customer relationship management (CRM) tools.
The back end is administrative. It is where admins, also known as privileged users, can perform tasks that affect the content and functioning of the system itself. This includes modifying the data displayed on the standard user interface or deleting customer records. A superuser with the highest privilege level can uninstall the CRM solution or delete its database.
Attacks like privilege escalation can be devastating, leading to costly remediation, data breaches, compliance penalties, and loss of customer trust. In many cases, the super admin level of privileges, often called “root access,” allows the attacker to erase logs, reinstall operating systems, and otherwise cover his tracks so no one will know how they got in.
Types of Privilege Escalation Attacks
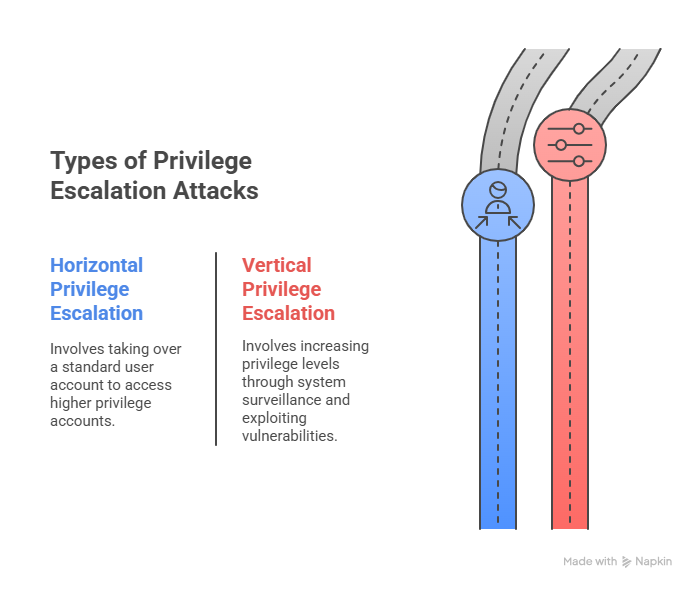
There are two basic types of privilege escalation attacks:
- Horizontal Privilege Escalation Attack
A horizontal privilege escalation attack is one in which an attacker takes over an account, usually a standard user’s. With this standard user account as a starting point, the hacker will usually try to take over additional accounts with higher privileges to access different feature sets and data.
- Vertical Privilege Escalation Attack
Vertical privilege escalation, in contrast, involves increasing the attacker’s privilege level. It typically includes a period of surveillance, during which the attacker observes how the system works, who’s on it, and how privileges are assigned. After surveillance, the attacker will move to exploit a vulnerability.
For example, the attacker might take advantage of an unpatched operating system vulnerability, such as the Linux “Dirty Pipe” (CVE-2022-0847) vulnerability, which allows an attacker to escalate his privilege level by manipulating the Linux kernel.
Common Security Gaps Leading to Privilege Escalation
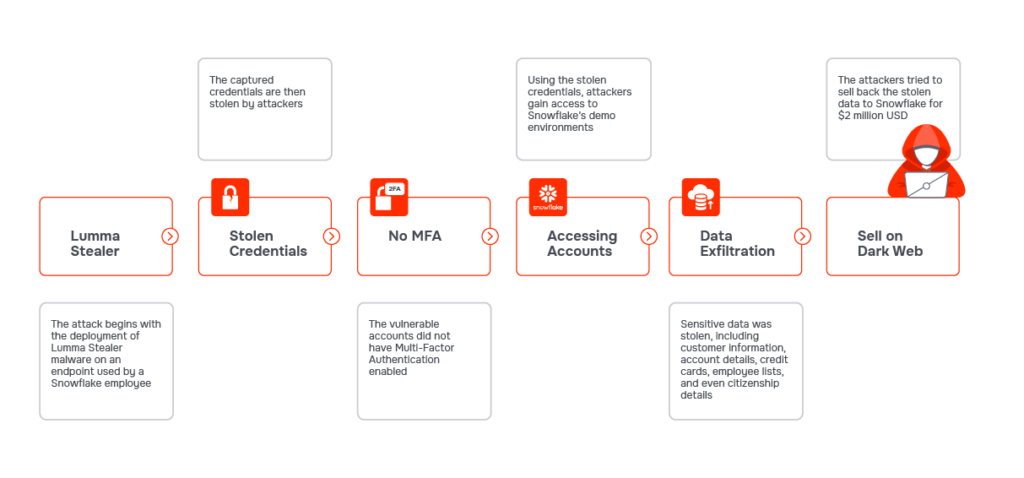
- Credential Exploitation
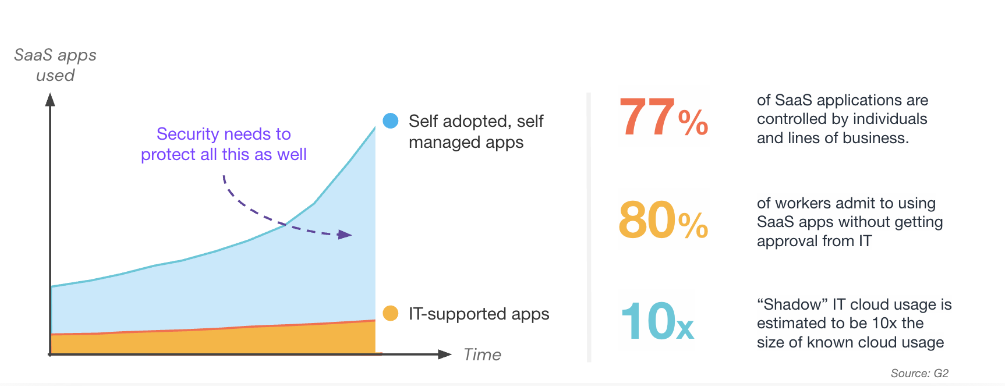
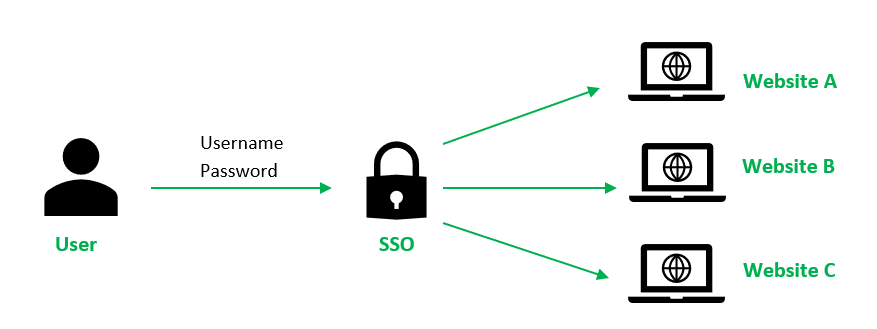
An attacker may be able to log into a target system using stolen credentials or simply by guessing a user’s password. Alternatively, they can run a brute force attack that discovers passwords by repeating trial-and-error attempts. This attack type assumes the system uses single-factor authentication (1FA). SaaS applications are often exposed to this risk if, for instance, users can set their security configurations and avoid multifactor authentication (MFA).
- Misconfigurations
A system’s configurations can expose it to a privilege escalation attack risk. Examples abound, but some of the biggest offenders are allowing simple passwords and 1FA and leaving systems with default security settings (a common mistake in SaaS applications).
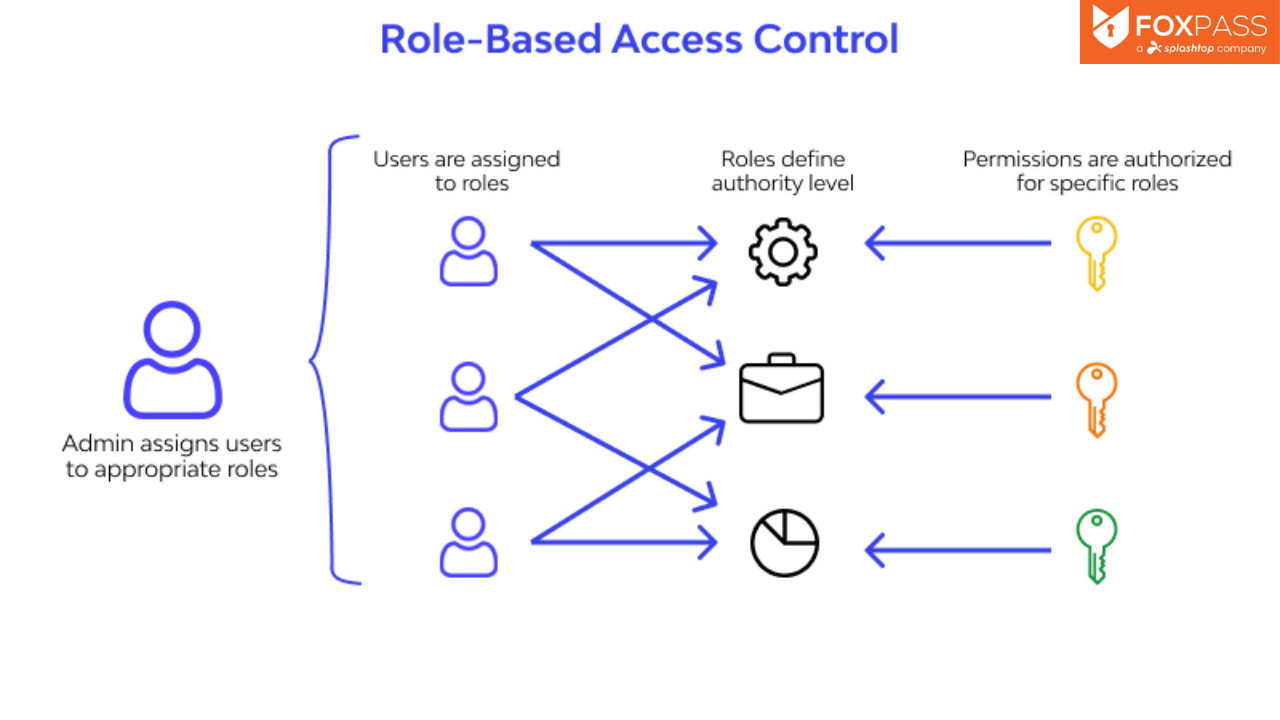
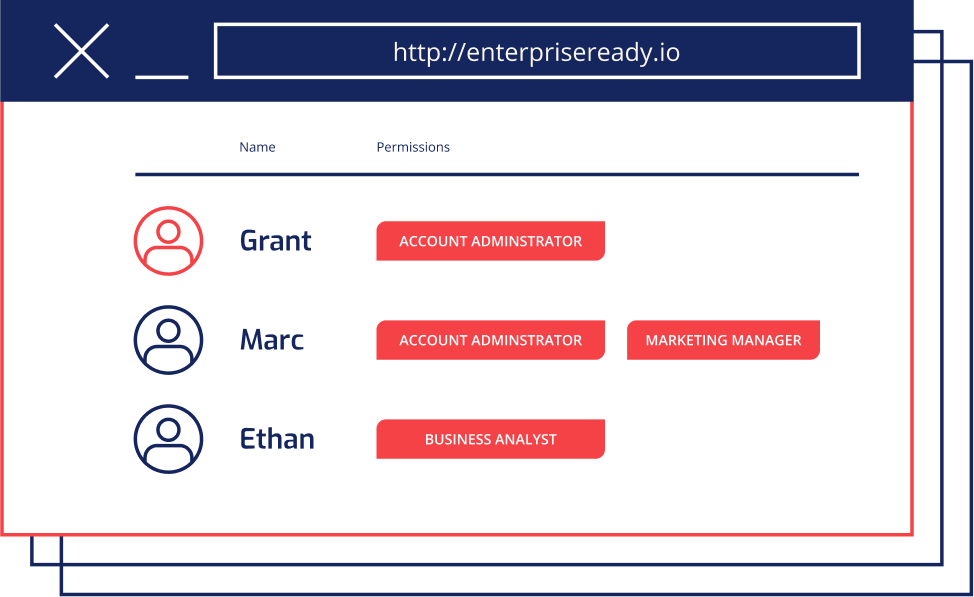
- Overly Permissive User Roles
Giving users excessive permissions can increase the risk of privilege escalation. For instance, a standard admin might inadvertently be granted super admin access, often due to staffing constraints or mismanaged roles.
In many enterprise applications, “Executive” users can access broader datasets than standard users, whose access might be limited by region or department. To simplify management, organizations may assign executive-level access to all users. However, this approach significantly raises the stakes: if an attacker compromises one of these accounts, the potential damage becomes much greater.
- Lack of Monitoring for Suspicious Activities
Many organizations fail to monitor user activity closely enough to detect insider threats or external signs of privilege escalation. Without real-time monitoring, anomalous behaviors (like logins at unusual hours or a new user rapidly gaining elevated privileges) can go unnoticed. This blind spot allows attackers to move laterally or escalate access without triggering any alerts, leaving systems vulnerable for extended periods.
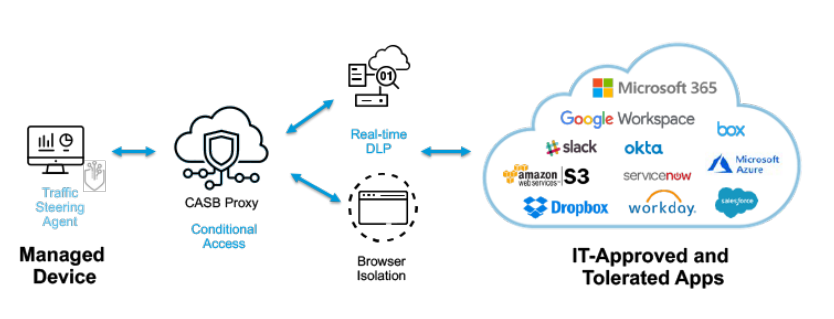
- Third-Party Integrations
Integrating with third parties, which is common in SaaS environments, can open the door to privilege escalation attacks. The SaaS app may treat the third party as a “user.” If security settings are not hardened or the third-party plugin has been compromised, the third party can be a vehicle for unauthorized privilege escalation.
How to Prevent and Mitigate Privilege Escalation Attacks
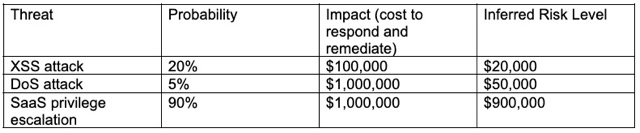
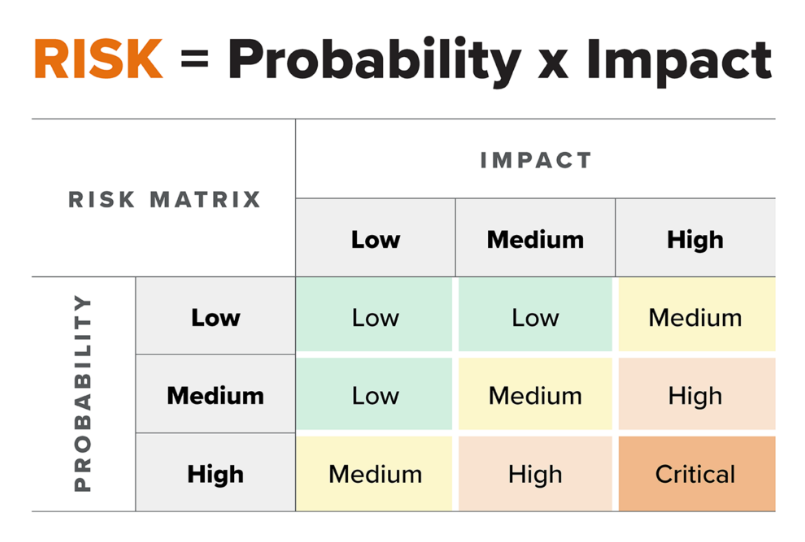
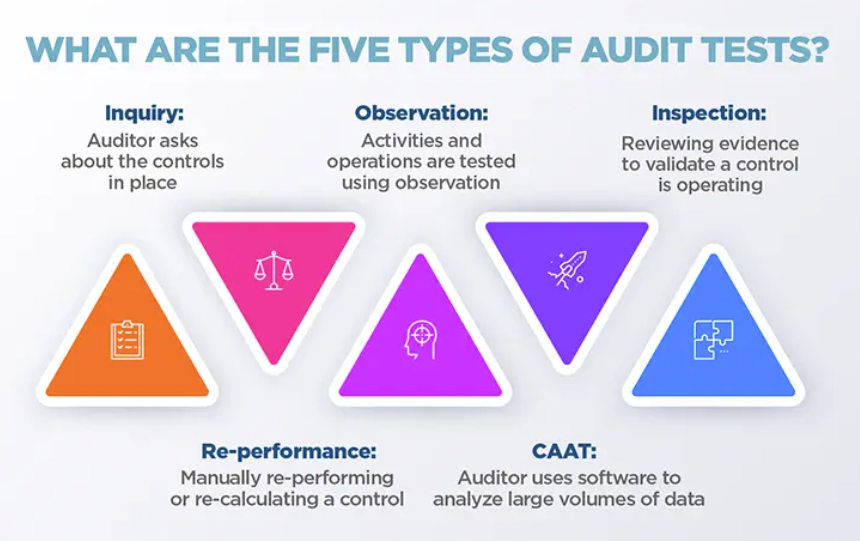
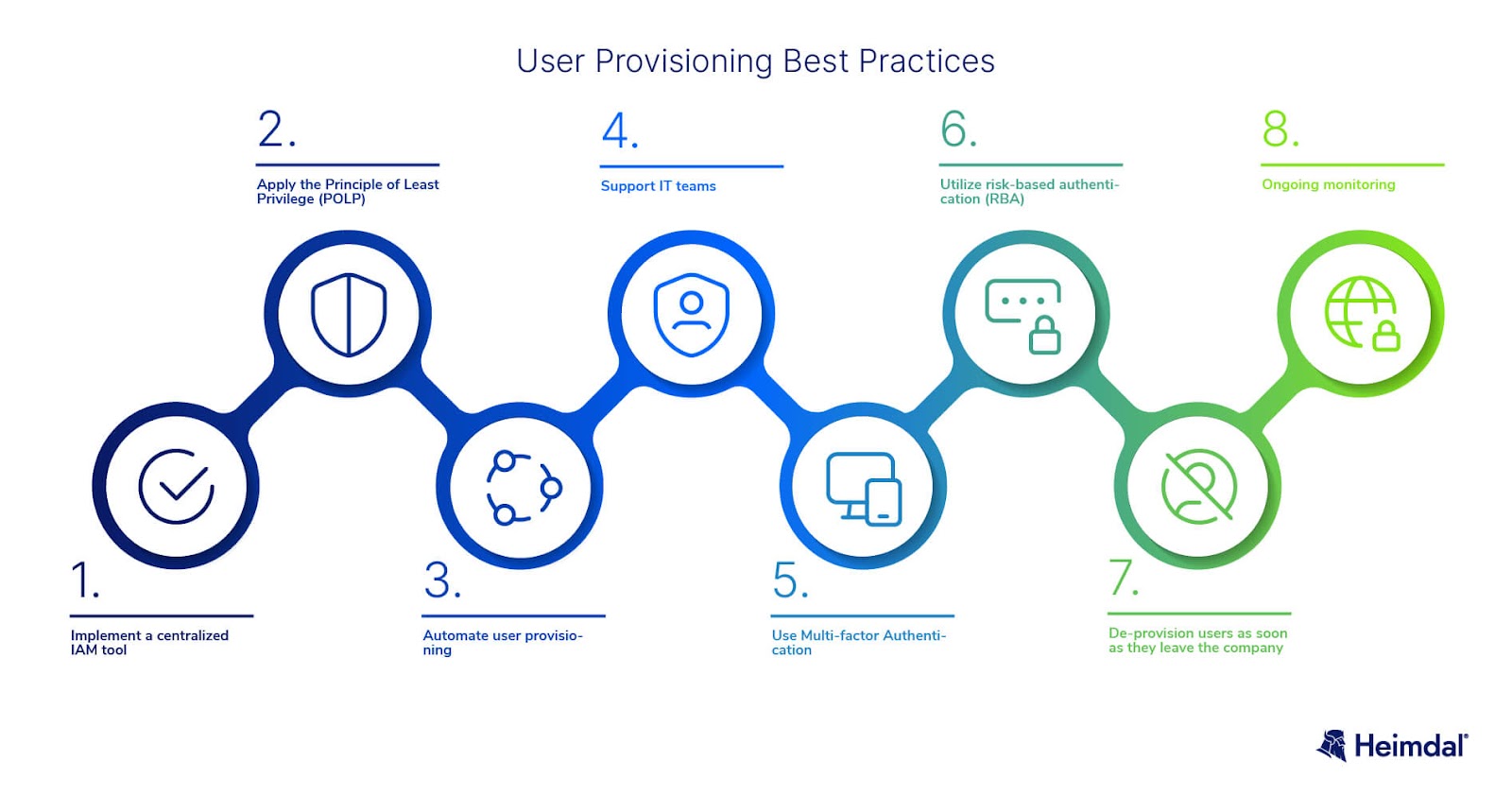
What can you do about privilege escalation attacks? Best practices fall into two broad categories: prevention and mitigation. Prevention is about setting up controls and countermeasures that reduce your risk exposure for privilege escalation. Mitigation, conversely, is about minimizing the impact of a privilege escalation attack. Here are some of the most popular prevention and mitigation best practices (some require purpose-built tools):
Prevention
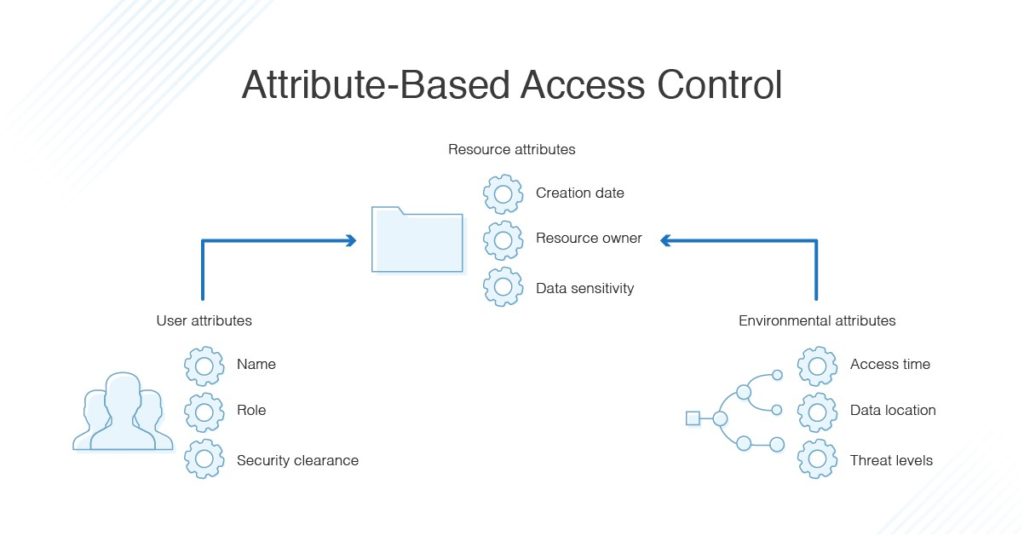
Attribute-Based Access Control (ABAC)
This approach to access control extends the traditional role-based access control (RBAC) model to a higher level of granularity, such as role hierarchies. Adding attribute-based access control (also called ABAC) limits role-based access by attributes like device location. Enforcing context-aware controls that restrict when, where, and how elevated permissions can be used minimizes the risk of privilege escalation.
Risk-Based Access Review
A periodical risk-based access review (usually quarterly) is critical to examine user access rights and verify that they are entitled to those privileges. It can often present unexpected findings, such as users who have left the company but still have access rights or who have changed roles but retained earlier access to systems they no longer need.
Continuous Misconfiguration Detection
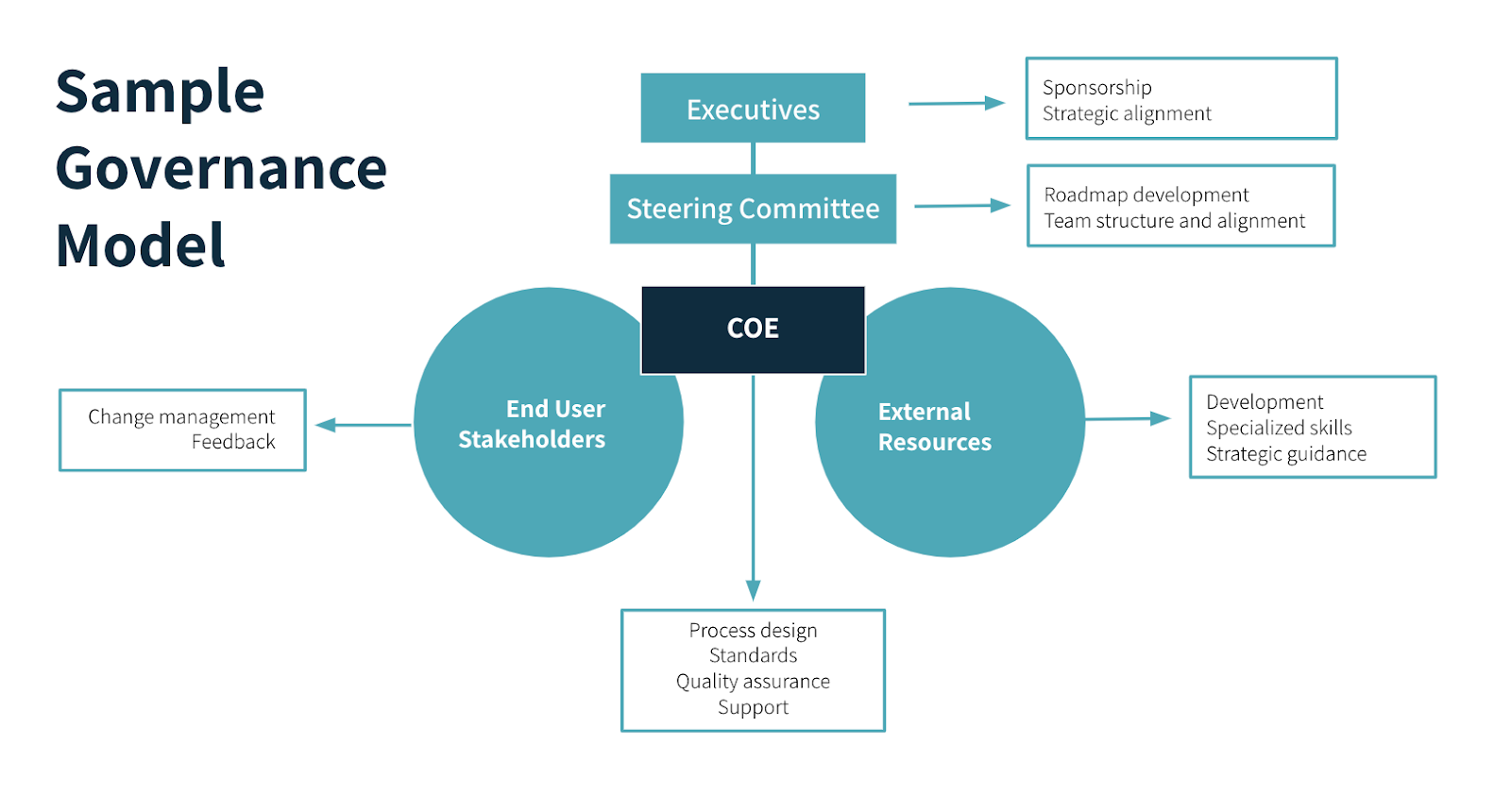
System misconfigurations are endemic to SaaS environments. A company might have a hundred SaaS apps running, each with unique security settings, making application dependency mapping incredibly challenging.
Solutions like Suridata can continuously monitor SaaS security configurations, detect insecure configurations, and alert admins to situations where they pose a risk for privilege escalation and other threats. When a misconfiguration is flagged, Suridata can also provide detailed remediation guidance.
Zero Trust Architecture (ZTA) Implementation
A Zero-Trust Architecture enforces the principle of least privilege and continuous authentication, reducing the likelihood of privilege escalation. Although ZTA minimizes the probability of privilege escalation, a sophisticated attacker can still work around it by impersonating users with high access privileges.
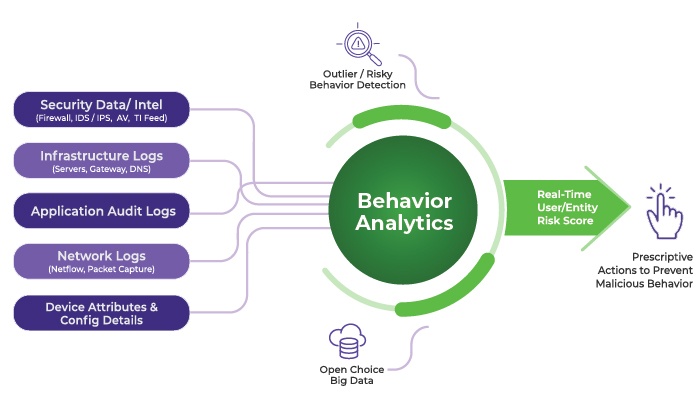
Behavioral Analytics for Insider Threat Detection
Insiders (such as employees or contractors) may carry out privilege escalation attacks due to resentment or a desire for revenge. To mitigate these risks, organizations should combine security testing with behavioral analytics.
Continuous penetration testing can help identify vulnerabilities that insiders might exploit, while AI-driven behavioral analytics can detect subtle patterns that indicate a potential threat.
Suridata can identify security threats of SaaS applications and enable rapid detection and mitigation of malicious privilege escalations.
Mitigation
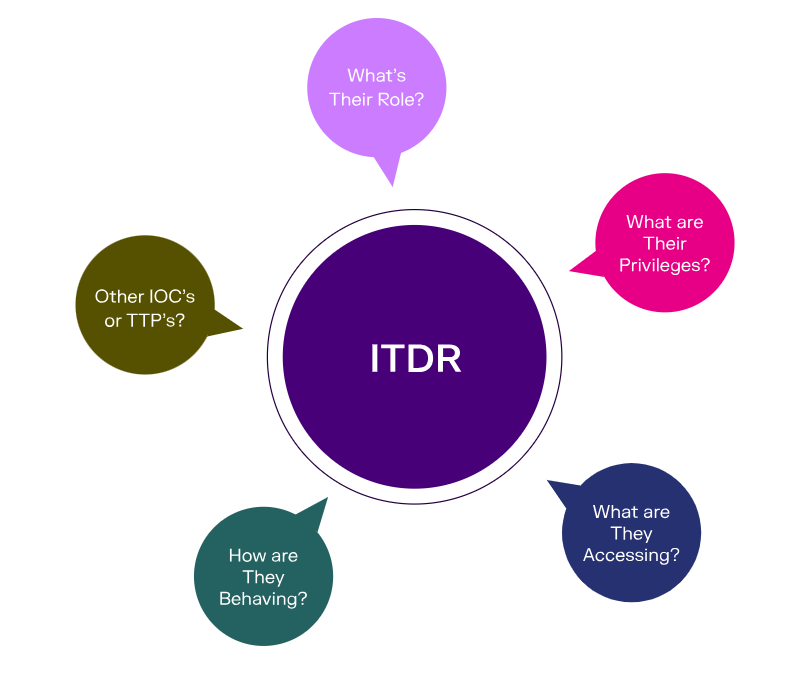
Real-Time Privilege Escalation Detection with Contextual Awareness
One challenge in mitigating privilege escalation attacks is differentiating between routine changes in privileges and those that come from attacks. Understanding context can make a big difference in distinguishing the good from the bad. For example, if a user’s access privileges are escalated across two departments two days in a row, that strongly suggests an improper context for the escalation.
Third-Party Integration Risk Assessment
Third-party integrations create unexpected back doors for privilege escalations, mainly for SaaS apps. Suridata can mitigate this risk by detecting insecure integration (for example, from plugins that contain known vulnerabilities or have not been patched) and flagging them for remediation. The platform also monitors user activities, analyzes access levels, and prioritizes risks for mitigation.
Risk-Based Multifactor Authentication (MFA)
Multifactor authentication is more effective when it adapts to risk signals. Instead of treating all access attempts the same, risk-based MFA evaluates the context, such as the user’s location, device, or access time.
For instance, the system can flag or deny the request if an OTP request comes from an unusual location or at an odd hour, like 2 AM on a Sunday. Zero Trust Architecture may also involve re-authenticating the user or device during an active session to ensure ongoing trust.
Incident Response for Privilege Escalation
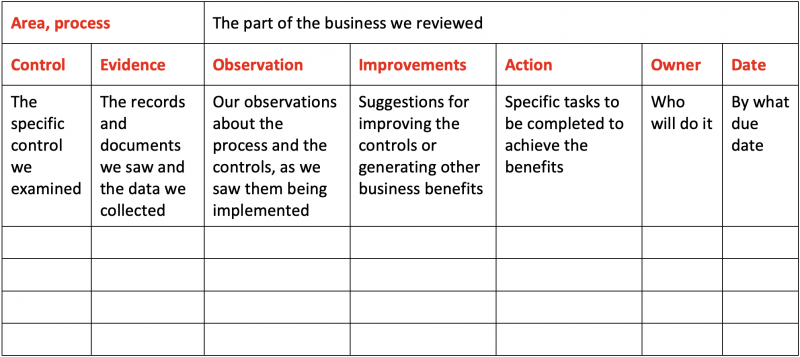
If a privilege escalation attack occurs, quickly contain the affected account, analyze logs for suspicious activity, revoke unauthorized access, and patch exploited vulnerabilities. Implement password resets, forensic investigation, and enhanced monitoring to prevent further compromise and strengthen security controls.
Protecting Access Privileges from Improper Escalation
Hackers often need to escalate their system access privileges to achieve their goals, and they resort to privilege escalation. They have many options available for privilege escalation, including social engineering, account takeover, and password theft. Once inside a system, they can exploit many vulnerabilities to gain back-end admin access or root control.
Privilege escalation attacks are a serious risk for the entire IT estate, but SaaS is a particularly problematic environment to defend. Many SaaS apps have their internal privilege hierarchy and difficult-to-monitor security configurations. Preventing and mitigating privilege escalation attacks in SaaS requires ongoing user behavior monitoring, visibility into third-party integrations, and continuous awareness of security configurations.
Suridata enhances SaaS security by detecting misconfigurations, excessive permissions, and third-party app risks, preventing privilege escalation attacks. Its automated remediation, real-time threat detection, and compliance support help enterprises strengthen their holistic SaaS security posture. Learn more at Suridata.
Co-Founder & CPO